SASE Hype and Reality: Our Key Takeaways From Gartner’s Hype Cycle Reports
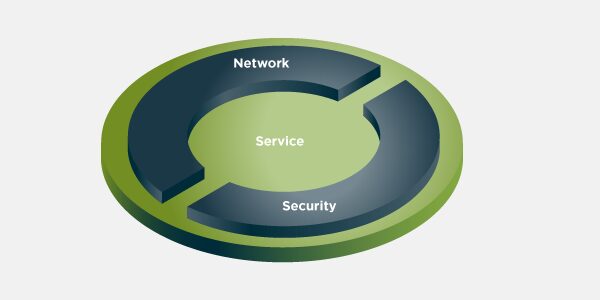
Secure Access Service Edge (SASE) has been a hot topic since Gartner first described it in 2019. As we see it, SASE aims to address one of the main business enablement issues of our time: how to provide performant, secure, just-enough access to applications anywhere, anytime by mobile, distributed workforces and devices. We view the SASE architecture as delivering tightly integrated network and security services like SD-WAN, NGFW, SWG, CASB, ZTNA, etc. to application flows on their optimal path — ideally through a distributed cloud infrastructure.
Gartner has recently published their observations and recommendations for SASE in three of their 2020 Hype Cycle reports: Hype Cycle for Endpoint Security, 2020; Hype Cycle for Network Security, 2020; and Hype Cycle for Enterprise Networking, 2020. The reports are must reads for those interested in understanding the current state of the coverage areas in general, and looking for practical advice on starting their SASE journey, in particular.
Here are my take-aways:
First, SASE is a genuine phenomenon. And not that new. Although the term was coined only in 2019, integrated network and security service offerings go much farther back. But since Gartner’s description, SASE has captured the imagination of vendors and enterprises alike. According to the reports, “by 2024, at least 40% of enterprises will have explicit strategies to adopt SASE, up from less than 1% at year-end 2018.”
But there’s still a lot of hype. Few vendors today provide truly integrated SD-WAN and network security services. The reports note, “there have been more than a dozen SASE announcements over the past 12 months by vendors seeking to stake out their position in this extremely competitive market. There will be a great deal of slideware and marketecture, especially from incumbents that are ill-prepared for the cloud-based delivery as a service model and the investments required for distributed PoPs. This is a case where software architecture and implementation matters.” I’ll second that. Many SASE services from larger vendors came via different acquisitions, and integration isn’t a given. Enterprise security and network leaders will have to do their homework; many will find that sourcing well integrated SASE services from a single vendor isn’t yet feasible.
So, most initial SASE implementations will involve more than one vendor. Gartner projects, “by 2023, 20% of enterprises will have adopted SWG, CASB, ZTNA and branch FWaaS capabilities from the same vendor, up from less than 5% in 2019.” That means 80% will implement using two or more vendors, and manage integration across services (presumably, on their own). Not very SASE but totally understandable.
In general, most enterprises will implement SASE in stages. Again, not a revelation. But on the question of how to go about doing SASE in stages, the SASE sections in the Hype Cycle reports provide what I consider to be practical recommendations.
When evaluating SASE offering, be sure to:
- Leverage a WAN refresh, firewall refresh, VPN refresh or SD-WAN deployment to drive the redesign of your network and network security architectures.
- Use cost-cutting initiatives in 2020 from MPLS offload to fund branch office and workforce transformation via adoption of SASE.
- Combine branch office and secure remote access in a single implementation, even if the transition will occur over an extended period.
- Prioritize use cases where SASE drives measurable business value. Mobile workforce, contractor access and edge computing applications that are latency sensitive are three likely opportunities.
- Strive for no more than two vendors to deliver all core services.
- Avoid vendors that propose to deliver the broad set of services by linking a large number of products via virtual machine service chaining.
My take on the recommendations is that you should use your upcoming projects as opportunities to move towards a SASE architecture; hold the line on the vendor sprawl; and ensure tight integration across services.
Last but not least, start looking at SASE services from various providers. The Hype Cycles name a few Sample Vendors in the SASE category. And I’m proud to say that Open Systems has been included! Check us out. We first rolled out our own integrated network and security stack that included SD-WAN, NGFW, VPN and SWG services in 2014 — before SASE and SD-WAN were even a thing. Our 8000+ fully managed deployments in over 180 countries are proof that with SASE is real and here at Open Systems.
Gartner:
Hype Cycle for Endpoint Security, 2020 (July 2020)
Hype Cycle for Network Security, 2020 (June 2020)
Hype Cycle for Enterprise Netowrking, 2020 (July 2020)
NOTE: Gartner does not endorse any vendor, product or service depicted in its research publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner research publications consist of the opinions of Gartner’s research organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this research, including any warranties of merchantability or fitness for a particular purpose.
Leave Complexity
Behind
To learn how Open Systems SASE Experience can benefit your organization, talk to a specialist today.
Contact Us